n8n offers two deployment options: the managed cloud service that n8n operates, and self-hosted deployment on your own infrastructure. For organizations with data sovereignty requirements, high automation volume, or compliance obligations that extend to their automation platform, self-hosted n8n is not an option — it is the requirement.
Self-hosted n8n is also the deployment that provides the most control: over the infrastructure it runs on, the data it processes, the security controls applied to it, and the cost model (no per-execution pricing). That control comes with infrastructure responsibility — the organization manages the platform rather than relying on n8n’s managed service.
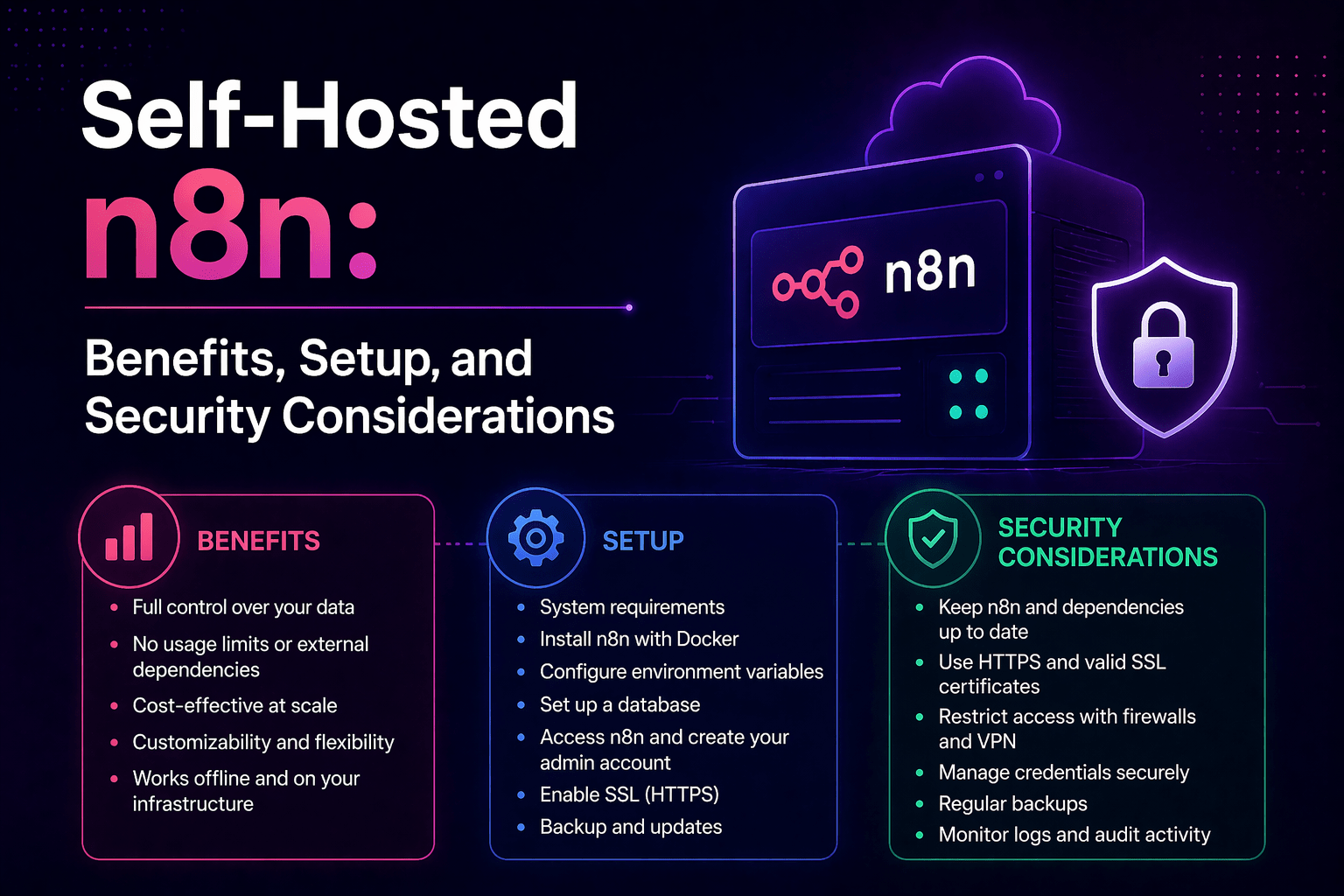
This guide covers the reasons to self-host, what deployment requires, and how to secure a self-hosted n8n instance correctly.
Overview
Self-hosted n8n deployment places the n8n automation platform on infrastructure the organization controls — cloud VMs, on-premises servers, Kubernetes clusters, or container environments. All workflow execution data stays within the organization’s infrastructure. There is no per-execution pricing. Security controls are applied at the infrastructure level by the organization’s IT and security teams. The organization is responsible for platform maintenance, updates, backup, and availability.
- Data sovereignty: all automation data stays on organization-controlled infrastructure
- No per-execution pricing: fixed infrastructure cost regardless of workflow execution volume
- Full customization: environment variables, database configuration, and infrastructure choices are organization-controlled
- Security control: the organization applies and manages security controls rather than relying on n8n’s managed service security
- Maintenance responsibility: updates, backups, and availability are the organization’s operational responsibility
This aligns with modern AI automation strategies and enterprise infrastructure control.
The 5 Why’s
Why do data sovereignty requirements specifically mandate self-hosted n8n for many organizations?
n8n workflows process the data that flows between connected systems — customer records, financial transactions, health information, proprietary process data. Cloud-hosted n8n processes that data on n8n’s infrastructure. Self-hosted n8n processes it on the organization’s infrastructure, subject to the organization’s data governance controls. For organizations subject to data residency regulations, HIPAA, financial data handling requirements, or contractual data handling obligations, self-hosting is the deployment model that satisfies those requirements.
Why does the per-execution pricing model specifically favor self-hosted deployment for high-volume automation?
n8n cloud pricing is based on workflow executions per month. For businesses with high automation volume — thousands or tens of thousands of executions daily — per-execution pricing produces monthly costs that scale with volume. Self-hosted n8n’s cost is infrastructure: servers or cloud compute that run at a fixed monthly cost regardless of execution volume. For organizations with significant automation scale, self-hosted total cost of ownership is typically lower than cloud pricing by a significant margin.
Why does self-hosted deployment require infrastructure planning that cloud deployment does not?
Self-hosted n8n must run on infrastructure that meets the performance and availability requirements of the automation it hosts. A workflow that runs once a day has different infrastructure requirements than one that processes 10,000 executions per hour. Infrastructure planning includes compute sizing, database configuration (n8n supports PostgreSQL for production deployments), queue management for high-volume workflows, and availability design for business-critical automation.
Why is database selection specifically important for self-hosted n8n production deployments?
n8n’s default SQLite database is appropriate for development and testing but not for production deployments at any significant scale. Production self-hosted n8n should use PostgreSQL — which provides better performance under concurrent load, proper transaction handling, backup capability, and the database management tools that production infrastructure requires. Organizations setting up self-hosted n8n for production should configure PostgreSQL from the start rather than migrating later.
Why does self-hosted n8n specifically benefit from a container-based deployment model?
Docker or Kubernetes deployment for n8n simplifies updates (pull a new image, redeploy), backup (database backups handled separately from application), scaling (additional workers for queue-based processing), and environment consistency (the same container configuration works in development, staging, and production). Container-based deployment also simplifies the security posture: the container runtime provides process isolation, and the container image version is explicitly controlled.
Self-Hosted n8n Deployment Options
Docker Deployment (Recommended for Single-Instance)
The simplest production self-hosted deployment:
- Docker and Docker Compose on a Linux server (cloud VM or on-premises)
- PostgreSQL container or managed PostgreSQL service for the database
- Reverse proxy (nginx or Traefik) for HTTPS termination and access control
- n8n container with environment variables for database connection, encryption key, and configuration
Minimum server requirements for standard production use:
- 2 vCPUs, 4GB RAM for moderate workflow volume
- Scale up for high-volume concurrent execution requirements
Kubernetes Deployment (Recommended for Scale)
- n8n Helm chart provides standardized Kubernetes deployment configuration
- Separate main n8n deployment and worker deployments for queue-based processing
- PostgreSQL via managed database service or Kubernetes-native deployment
- Horizontal pod autoscaling for worker deployments to handle variable execution load
Cloud VM Deployment
- n8n installed via npm on a Linux VM
- Managed PostgreSQL from cloud provider (RDS, Cloud SQL, Azure Database)
- Systemd service for n8n process management
- Load balancer for HTTPS termination
Security Considerations for Self-Hosted n8n
Access Control
- n8n should not be publicly accessible without authentication
- SSO integration configured where available
- MFA enforced for all users
- Network access restricted to authorized IP ranges or VPN
- Admin access limited to minimum required users
Encryption
- HTTPS enforced for all access
- Strong encryption key configured and securely stored
- Database connections use SSL/TLS
- Backup data encrypted at rest
Updates and Patching
- Monitor n8n releases for security updates
- Test updates in staging before production
- Apply updates consistently across platform components
Backup and Recovery
- Daily database backups
- Periodic backup restoration testing
- Defined recovery time objectives
Credential Security
- Encryption key backed up securely
- Stored in secrets management system
- Loss of key results in loss of credentials — must be protected
Final Takeaway
Self-hosted n8n gives organizations the data control, cost structure, and infrastructure customization that cloud deployment cannot provide. It requires infrastructure planning, security configuration, and operational maintenance that cloud deployment handles automatically. For organizations with data sovereignty requirements, high automation volume, or compliance obligations that extend to their automation platform, the control self-hosting provides is worth the operational investment. Getting the deployment and security configuration right from the start is significantly less effort than addressing gaps discovered after sensitive data has been flowing through a misconfigured instance for months.
Deploy and Secure Self-Hosted n8n With Mindcore Technologies
Mindcore Technologies designs and deploys self-hosted n8n infrastructure — architecture selection, PostgreSQL configuration, container deployment, security hardening, monitoring setup, backup configuration, and ongoing platform management that produces a production-reliable, security-appropriate n8n deployment.
Schedule your free strategy call to design your self-hosted n8n infrastructure and ensure it meets your performance, security, and compliance requirements.