Spear Phishing Defense Resources
Spear phishing is a type of social engineering scam in which a perpetrator tricks a user into providing sensitive information, sending money, or downloading malicious software. Among the many forms of phishing, spear phishing remains the most popular avenue for attack, used by 65% of all known threat actors.
What is Spear Phishing?
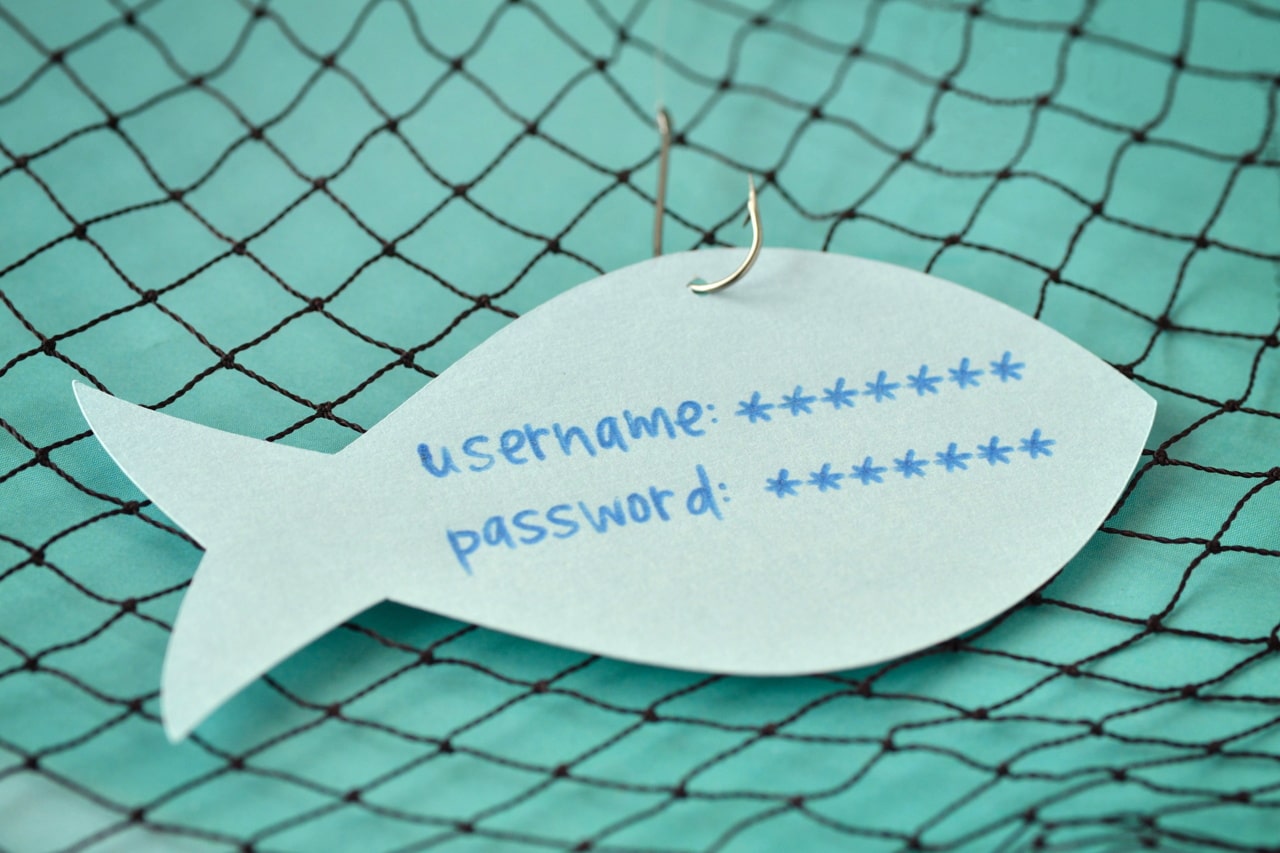
Spear phishing is a highly customized email targeted at a specific individual or department in a company that appears to be from a trusted source. The goal of spear phishing is to steal data, such as login credentials, or infect the user’s device with malware. Typically, the attacker will carefully research their targets and use various social engineering techniques to urge the victim to click on a dangerous link or attachment. Once clicked, the attacker can gain access to the network undetected.
While phishing has been around since the 1990s, spear phishing is a much more recent phenomenon. The first notable cases of spear phishing attacks date back to 2010. Between 2010 and 2011, these attacks grew by 300%. If a spear phishing attack is successful, stolen usernames and passwords may be used to compromise company email and financial systems and breach other software tools.
The Difference Between Phishing, Spear Phishing, and Whaling
While phishing and spear phishing attacks share similar traits, there are many key differences. A phishing campaign is broad and automated, and it doesn’t take a lot of skill to execute. On the other hand, spear phishing and whaling are very targeted, going after a specific employee, department, or individual in an organization. See how each type of attack works below.
Phishing
Phishing campaigns often have no specific target and they prioritize quantity. The messaging is generic and sent to a large number of individuals or organizations in hopes of “catching” a victim. Standard phishing is effective for smaller payouts, like credit card data, usernames, and passwords, and is usually a one-and-done attack.

Spear Phishing
Spear phishing attacks prioritize quality over quantity. They take a more targeted approach than phishing for bigger gains. Spear phishing attacks are more likely to deceive potential victims due to the amount of research and time spent personalizing messages to appear legitimate.

Whaling
Whaling, also known as CEO fraud, is when an attacker targets one or more C-level executives. It uses the same personalized strategy as spear phishing but goes after senior management, who has high-privilege account permissions on the network, to expose financial and confidential information.

How to Identify Spear Phishing
Although the majority of spam emails are easily identifiable, spear phishing is much harder to detect. In fact, as many as 95% of all attacks on enterprise networks are the result of successful spear phishing. They may look like legitimate emails from a trusted person, such as a friend, coworker, or boss. It’s important to understand the telltale signs of a spear phishing attack to protect yourself and your organization as a whole.
A commonly used tactic in spear phishing involves sending an email from a domain name that looks like a well-known business but isn’t. Letters can be misused to fool unsuspecting users. For example, the lowercase letters “r” and “n” next to each other can look like the letter “m” at first glance.
Subject lines in spear phishing emails attempt to evoke a sense of urgency or fear to prompt the victim to act quickly. Common red flags include using words like “Important” or “Urgent” to garner attention. Some scams may even use language such as “Re:” or “Fwd:” to make it seem like a conversation has already occurred.
Spear phishing emails often include embedded malware in the form of .zip files, .exe files, PDFs, Excel, and Word documents. Look at who the email came from to check the validity of the link or attachment. You should also be wary of forms, such as Google Forms, that request sensitive information.
A spear-phishing email usually contains your personal information to some degree. Remember that scammers can find your address and phone number, names of family members, and even pet names from public records and social media accounts.
How to Prevent Spear Phishing
There is no single approach to defend against spear phishing, but having an airtight cyber security plan is a great place to start. Spear phishing scams are particularly effective because they’re designed to get around traditional spam filters. To prevent spear phishing, you need to deploy a combination of technology and user security training. Here are five best practices businesses should consider, to combat these types of attacks.
Security awareness training is fundamental to prevent spear phishing. Employees need to be trained regularly on how to recognize and report common attacks, such as through phishing simulations. Knowledge is power, but only if you use it correctly.
Multi-factor authentication significantly reduces the impact of spear phishing. MFA adds an extra layer of security so that, even if a password is compromised, it’s useless without the additional authentication steps. Don’t reuse the same password across multiple accounts.
Having loose, or non-existent, password management puts your business at serious risk. You should require users to create unique and complex passwords and change them at certain intervals. You can also implement software, such as LastPass, to safely store passwords.
Running regular backups and installing security patches is imperative for the best defense against spear phishing. It’s almost impossible to recover your data after a breach if there are no backups to restore. You should also install security patches as they become available to ensure your software is always up to date.
Email security software is used to identify common attack signals over email and other cloud applications and remediate threats before they cause damage to your business. Investing in this type of software is your best bet in derailing spear phishing attempts.

Meet our CEO, Matt Rosenthal
With over 30 years of experience in cybersecurity and IT leadership, Matt Rosenthal brings a strategic, executive-level perspective to threats like spear phishing attacks that target organizations at their most vulnerable points, people and access. As CEO of Mindcore Technologies, he has led the development of security frameworks that focus on identity protection, user awareness, and proactive threat prevention. His leadership ensures cybersecurity is not treated as a reactive measure, but as a structured defense strategy designed to anticipate and neutralize attacks before they succeed.
For organizations navigating the risks of spear phishing, Matt’s expertise centers on reducing human-based vulnerabilities through layered security and continuous monitoring. These attacks are often highly targeted and difficult to detect, making employee awareness, email security controls, and access management critical components of defense. Under his leadership, Mindcore helps businesses implement security strategies that protect against credential compromise, prevent unauthorized access, and strengthen overall resilience against advanced phishing threats.
Spear Phishing Frequently Asked Questions
Spear phishing, as the name suggests, involves attempting to catch a specific fish. The emails include personal information about the user to convince them to take action. All spear phishing is targeted, but sometimes focused on less prominent targets with an important function in the company.
Spear phishing is one of the most popular methods of attack used by hackers. In addition, over 90% of all cyber-attacks and data breaches start with a spear phishing attempt. These scams are not difficult or expensive to carry out, as the attacker can easily gather necessary information from social media, company websites, etc.
There are several ways to protect your organization from spear phishing, including security awareness training, multi-factor authentication, regular backups, and patch management. The more policies and procedures you have in place, the better prepared you’ll be when a threat arises.
In 2020, 66% of organizations worldwide saw spear phishing attempts. However, some industries and departments are more likely to be targeted than others. Businesses that operate in the technology, healthcare, manufacturing, and legal sectors, and those in high-ranking positions, are usually targets of spear phishing.
Spear phishing is far more successful than the non-targeted efforts of generic phishing attacks. A 2021 report from FireEye found that spear phishing emails had an open rate of 70%, with 50% of recipients clicking on embedded links. Many users fall for spear phishing because of its highly personalized nature.